Introduction
Organizations in today’s digital world hold data of their customers and clients which makes them a target for hackers, Organisations must follow robust cyber security policies/standards/guidelines to protect themselves, their employees, and most importantly their data against a wide range of threats. A Information security checklist helps organizations keep a track of their cyber security health to make sure an attacker cannot get unauthorized access to information that is stored on devices such as servers, databases, cloud, workstations, etc.
Cyber incidents are on the rise, organisations are continuously attacked by threat actors that can range from lone wolfs to nation-state actors. Phishing attacks are one example of such attacks. Ransomware is one of the top threats, where an attacker uses a malicious program to encrypt the entire data of the computer/workstation and makes it unusable unless a decryption key is purchased from the attacker or in other words unless a ransom is paid.
Before we jump to the Information security checklist on how to protect your organization, we must understand the threats to an organization, without proper identification of threat sources, we would not be able to develop or implement cyber security guidance properly.
Top Threats to organizations
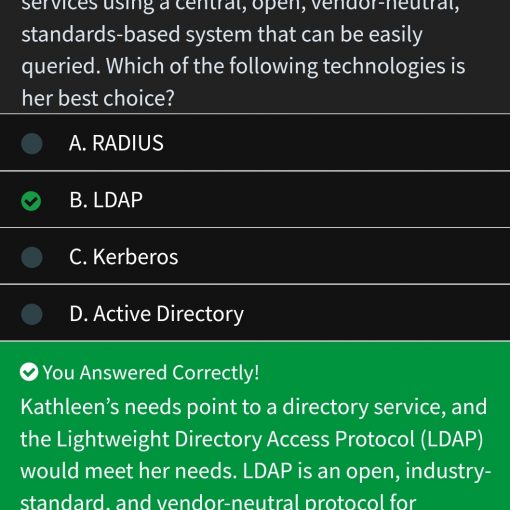
 |
Ransomware Malicious programs that make data or systems unusable until the victim purchases its decryption key. Most modern Ransomware malicious software is undecryptable. Regular backups are one of the important ways to protect against ransomware attacks. |
 |
Phishing campaigns send large amounts of emails to many people asking for sensitive phishing is a targeted phishing campaign launched against an organization or individuals. information (such as credit card details) or force them to visit scamming websites. |
 |
Virus is malicious software that can self-replicate and is developed to infect legitimate systems.
Malware is a piece of executable, that infects, explores, steals or conducts virtually any behaviour an attacker wants. Malware usually has the objectives to steal data, provide remote control of infected system and perform spam. |
 |
Insider Risks The potential for damage to be done maliciously or inadvertently by a legitimate user with privileged access to systems, and network data. Insider threats from your employees intentional Or unintentional is one of the growing threats to organizations. Insider attacks are very hard to detect since an insider already has access to the organization |
Information security checklist for Small to Medium Organizations
Cyber Security Control | YES | No |
Non-disclosure agreements – Ensure confidentiality or non-disclosure agreements with contractors and external entities. | ||
Risk Assessments – A periodic activity is ensured to manage the cyber security risk to organisation’s business. Risk assessment activity help in determining the current risks, their impact, severity, lose expectancy | ||
System Security – A documented process to ensure that security requirements are in place for systems, it also makes sure that controls are in place to protect those systems. | ||
System Certification – A process in place to make sure the existing or new systems are being tested for potential security issues. Technical assessment can be conducted using a variety of automated tools available to make sure consistency. Higher management and operational management must be involved in this process. | ||
Configuration Change Control – Any changes that are made to an organisation's systems must go through a change management process that takes care of formally introducing change to systems/processes. Change management process is a list of activities that must be performed before any change is allowed. | ||
Vulnerability Scanning – Vulnerability scanning of assets to find out pending vulnerabilities that are present in the systems which needs to be triaged. This activity must be performed periodically to make sure systems/applications remain up to date. | ||
Human Resources Security – Policies and procedures in place to make sure the employees are in compliance with the rules and regulations. | ||
Third Party or Contractor Security – Individual security requirements for contractors and third party employees are in place. Such requirements are usually finalised in service level agreements (SLAs) | ||
Individuals Screening – Employee screening and background check is performed to verify and legitimise the employee before granting access. | ||
Physical Access Monitoring – Monitoring of physical area is ensured, this involved the outside and inside of the physical premises of the organisation this also includes data centres as well. Areas are monitored and movements are logged in, those logs are periodically reviewed for any violations. Logs must be kept safe and secure. | ||
Physical Access Control – Physical access to organisations containing information systems is controlled and individuals’s authorization is verified before granting access. | ||
Secure Disposal of Equipment – Processes and procedures in place to securely dispose of information and equipment. | ||
Disaster Recovery Planning – A Disaster Recovery Plan (DRP) is in place that supports the current business continuity needs of the agency. The DRP plans for the recovery of technology and communications following any major event that disrupts the normal business environment, provides for periodic updating and testing of the plan, and its documentation includes, but is not limited to: | ||
Recovery based on critical and sensitive business needs. | ||
Location of regular backups of systems and data, with documentation. | ||
frequently updated information about where copies of the plan reside, including appropriate off-site locations. | ||
Training for appropriate individuals. | ||
Information Back-up – Backup copies of information and software are completed on a routine schedule, tested frequently, and stored off-site. | ||
Monitoring – System logging, and routine procedures to audit logs, security events, system use, systems alerts or failures, etc. are implemented and log information is in placed where it cannot be manipulated or altered. | ||
Data Classification – Policies and processes to classify information in terms of its value, legal requirements, sensitivity, and criticality to the organisation are in place. | ||
Access Controls – Access control policies and procedures to ensure appropriate level of access is achieved in a secure way. | ||
Password policies in place such as password rotation, length and complexity of passwords, Using Multi Factor authentication etc. | ||
Security of Wireless access points. | ||
Secure remote access procedures and policies are in place, and are known and followed by users. | ||
Protection of BYOD resources through policies and procedures. | ||
Tracking and periodic review of access granted. | ||
Access to network components either from users to services is authenticated before assigning access. | ||
Least Privilege – Ensuring that for any user or system service only provide the minimum access it requires to perform the desired activities for running the operational end of the business. | ||
Data Storage and Portable Media Protection – | ||
Identification and Authentication – Policies in place to address the identification and authentication of roles and responsibilities. | ||
User Identification and Authentication – Unique identification of users using username/password to systems/applications. | ||
Device authentication and identification – Identification of systems and devices before assigning roles, access to data or other systems. | ||
Malicious Code Protection – A regular patching process has been implemented to protect against malicious code. The process is automated when possible. | ||
Intrusion Detection – Tools and techniques are utilised to monitor intrusion events, detect attacks, and provide identification of unauthorised system use. | ||
Security Alerts and Advisories –. Security operations team receives notifications on latest emerging threats through threat intelligence feeds. These feeds are then incorporated into the security auditing and monitoring. | ||
Information Security Governance – Senior Management has designated roles and responsibilities for information security across its organisation. It included documenting, and regularly updating a formal information security program that addresses purpose, roles, responsibilities, scope applicable purpose, laws and regulations, and the implementation of policies, standards, and procedures. | ||
Perform threat modelling in the design phase of SLDC to make sure you find threats as early as possible within the SDLC, Finding threats early in the software development lifecycle helps you save costs in terms of time, finances and more importantly possible reputational damage. |