Introduction Application Threat Modeling using DREAD and STRIDE is an approach for analyzing the security of an application. It is a structured approach that enables you to identify, classify, rate, compare and prioritize the security risks associated with an application. Application Threat modeling should be considered separate from Risk Assessment, although similar but Application Threat Modeling is more of a calculated approach. Inducing Application Threat Modeling into SDLC process has its advantages for the security of the entire project. Most importantly when performing security assessments following the threat modeling approach gives the reviewer a comprehensive overview of the Application. This […]
Monthly Archives: October 2017
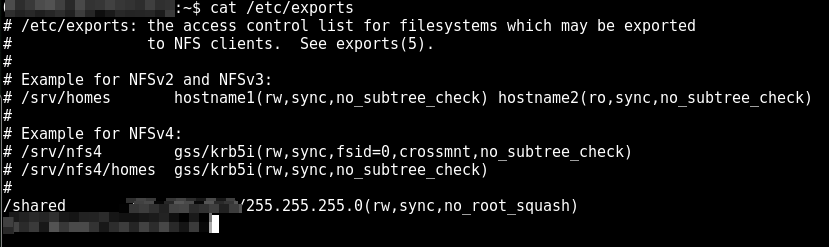
Recently during a penetration testing assessment I was able to get Linux Privilege Escalation using weak NFS permissions in “/etc/exports”. Initially I got a restricted shell access with limited permissions by exploiting a vulnerable service. Started to recon for privilege escalation to root access but couldn’t get the “usual suspects” (Kernel Exploits, vulnerable services etc). Having no further progress for linux privilege escalation I went back to my pre-limitied shell recon results, its important to mention that penetration testers when they get the initial shell access often don’t look back at recon results and start gathering only the internal information about […]
During web application security assessments, Cross Site Request Forgery is often an underrated vulnerability and often ignored, either due to the fact that it requires some sort of user interaction or lack of severity. Lack of severity part is debatable, it depends on which functionality the CSRF vulnerability exists, for example it would be severe if it exists on a password change functionality, an attack could send a crafted link to victim, victim clicks the link (Actual click is not required, one could use embedded HTML links in a page), attacker rides the victims session and password gets changed of […]