Introduction I have been doing Bug bounties for over 8 years now as a researcher on different platforms (Hackerone, Bugcrowd, Synack etc) but recently I had recent experience in bug bounties from the other side of the table, from the program side. After conducting the feature assessment and POCs of major platforms (an activity spanning over three months) I would like to share my experience which would hopefully help you choose the “right” platform to achieve your bounty objectives. This Bug Bounty Platform Comparison post focuses on why you need a bug bounty platform, criteria, and considerations in choosing the […]
Appsec
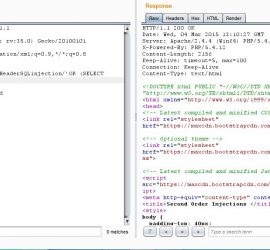
Introduction This post is the second in a series of noob-friendly posts that I am doing on SQL injection. Earlier I explained Second Order SQL Injections with Example. So in this post, I will be explaining the HTTP header Blind SQL injection, I prepared a Demo for the HTTP header Blind SQL injection For Example, HTTP has many reserved header fields the header I am choosing for the demonstration is the referrer header. What is HTTP Referrer Header? A referrer header is an HTTP header field, it’s simple job is to identify where the request originated from, for example, if […]
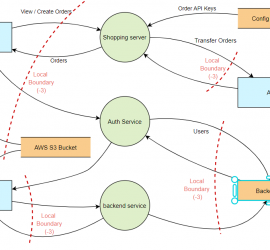
STRIDE Threat modelling Which THREAT modelling framework/methodology should I go for? This is a very common question nowadays, since the “Shift-left revolution”, we have all been trying to introduce security as early into the SDLC as possible (if we aren’t? we should!). THREAT modelling is the foundational activity of shifting left, which basically means finding threats early into the SDLC. Finding threats early in the software development lifecycle helps you save costs in terms of time, finances and more importantly possible reputational damage. Now that you are sold on doing threat modelling in the design phase of SDLC, the question […]
Introduction Sometime back I was hunting for Vulnerabilities in Microsoft Web services, as Microsoft has large online infrastructure, finding a vulnerability which could lead to Microsoft hall of fame for security researchers wasn’t difficult. While browsing around their online services, one of their services, Microsoft hub translator caught my attention. Microsoft hub translator is and I quote: “Microsoft Translator Hub empowers businesses and communities to build, train, and deploy customized automatic language translation systems—-”. I signed up and started looking for vulnerabilities and found critical level vulnerability through which I was able to delete All Microsoft hub translator 13000+ projects. As the vulnerability is fixed now, I’m sharing […]
Introduction Second Order SQL injection is an application security vulnerability, it occurs when user-submitted values are stored in the database, and then it gets used by some other functionality in the application without escaping or filtering the data. Usually, data from external sources (user supplied) is considered dangerous and is escaped/filtered. Developers trust the data coming from the database. This behavior is similar to a Stored Cross Site Scripting attack. Second Order SQL Injection requires more knowledge of how submitted values are later used in order to perform successfully second-order SQL injection. Still confused? follow the example below:- Second Order […]
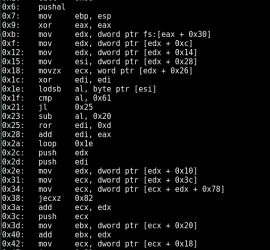
How many lines of code it takes to convert Hex to Assembly? only FIVE Thanks to Python and Capstone!. During binary analysis, exploit development or reverse engineering you require a quick dissembling of hex shellcode to assembly. You could do that using a dissembler like Ollydbg or IDA Pro, if you don’t want to use a full fledged dissembler to perform this small task the following code will help to convert hex to assembly using simple python script. Firstly if you don’t already have capstone you need to install it using the following:- Debian based Download and install using the following […]
Introduction Application Threat Modeling using DREAD and STRIDE is an approach for analyzing the security of an application. It is a structured approach that enables you to identify, classify, rate, compare and prioritize the security risks associated with an application. Application Threat modeling should be considered separate from Risk Assessment, although similar but Application Threat Modeling is more of a calculated approach. Inducing Application Threat Modeling into SDLC process has its advantages for the security of the entire project. Most importantly when performing security assessments following the threat modeling approach gives the reviewer a comprehensive overview of the Application. This […]
During web application security assessments, Cross Site Request Forgery is often an underrated vulnerability and often ignored, either due to the fact that it requires some sort of user interaction or lack of severity. Lack of severity part is debatable, it depends on which functionality the CSRF vulnerability exists, for example it would be severe if it exists on a password change functionality, an attack could send a crafted link to victim, victim clicks the link (Actual click is not required, one could use embedded HTML links in a page), attacker rides the victims session and password gets changed of […]