Introduction During Penetration testing engagement you are required backdooring PE file with your own shellcode without increasing the size of the executable or altering its intended functionality and hopefully making it undetectable (UD) how would you do it?. For example, after recon, you gather information that a lot number of employees use a certain “program/software”. The social engineering way to get in the victim’s network would be a phishing email to employees with a link to download “Updated version of that program”, which actually is the backdoored binary of the updated program. This post will cover how to backdoor a […]
Monthly Archives: November 2017
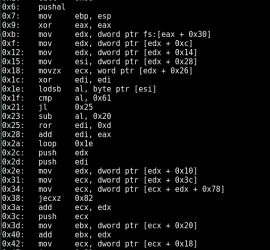
How many lines of code it takes to convert Hex to Assembly? only FIVE Thanks to Python and Capstone!. During binary analysis, exploit development or reverse engineering you require a quick dissembling of hex shellcode to assembly. You could do that using a dissembler like Ollydbg or IDA Pro, if you don’t want to use a full fledged dissembler to perform this small task the following code will help to convert hex to assembly using simple python script. Firstly if you don’t already have capstone you need to install it using the following:- Debian based Download and install using the following […]
In software development they say “Clients don’t even know what they want, they just want it and want it now!” no wonder they keep showing them prototypes. The case is similar in Information security as well, they just want it “secure”. As a penetration tester when you go out to perform Penetration testing engagement, you must have a clear mind on what the client wants. What are the do’s and don’t? What matters to them the most? Chances are that even if you performed technically sound pentest, they would still not be pleased. Maybe it’s the “first time getting their […]